Maplewood Career Center
7075
State Route 88 Ravenna, Ohio
Electronic Crime in Today's Society
Instructor
Roger F.
Cram
Cell phone: 330-569-4912, rfcram@aol.com
Fall 2017
Class Meeting Times and Dates (16 three-hour class sessions)
6:00 pm to 9:00pm
Monday, September 25; Wednesday, September 27; Monday, October 2; Wednesday,
October 4; Monday, October 9; Wednesday, October 11; Monday, October 16;
Wednesday, October 18; Monday,
October 23; Wednesday, October 25; Monday,
October 30; Wednesday, November 1; Monday, November 6; Wednesday, November 8;
Monday, November 13; Wednesday, November 15
Abbreviated Course Syllabus
Text Books
Technologies, Social Media, and Society - 13/14 Edition or the Twentieth Edition
Managing The Risk of Fraud and Misconduct
- McGraw Hill
-
After completing this course
you should be able to...
...understand the principles of stolen identity, credit card fraud, slander
on Facebook, email flaming, etc
...be aware of the changes in corporate
cultures that provide opportunities for internal crime and the employee
stress that encourages such activity in addition to developing affective
anti-fraud measures
...explain how induction and magnetic provide an
opportunity for electronic secrets to be intercepted and stolen
...detail the
history and modern-day electronics involved as hackers, phreakers, and telephone
criminals go about their trade stealing information in this digital age.
...discuss various forms of electronic occurring in corporations, various governments, different
branches of our military, several
...research and development firms, social
media, and political arenas.
...understand what motivates people to commit corporate crime, what kinds of behavior and personalities indicate potential criminals, which personality
characteristics are indicative of anti-
social behavior, and what
cultures may even encourage crime.
...help protect their vulnerability to
hackers intercepting their email, cell phone messages, texts, WI-FI,
Bluetooth signals, Ransomeware attacks, phishing, and cybersquatting,
Session 1
Introduction:
Class topics, areas covered, scope of course, rules
at Maplewood
Electricity:
Atoms and magnetic fields
Management:
Understanding Fraud
Hacking History: Telephone Fraud - The Invisible
Criminal
Current Events: The Five Things We
Need to Know about Technology
Vocabulary:
words assigned
Other:
Session 2
Electricity: Frequency and light
Management: Asset Misappropriation
Hacking History:
Current Events:
Vocabulary: None
Other:
Session 3
Electricity: Radio Waves;
Ohm's Law - Charge,
Current, Voltage, and Resistance
Management: Reporting Financial Fraud, the Fraud
Triangle
Hacking History: RFID Wallets and
Readers (Radio Frequency Identification)
Current Events:
Facebook and Google
Vocabulary:
words assigned
Other:
Session 4
Electricity: Induction
Management:
Falsifying Government Claims and Insider
Trading
Hacking History: Kevin Mitnik
Current Events: Creating Safe Passwords
Vocabulary: None
Other:
Session 5
Electricity: Transformers
Management:
Phishing and cybersquatting
Hacking History: Video:
Hackers
Current Events:
Discussion
- How Modern
Technology Has Negatively Impacted Your Life
Vocabulary: words assigned
Other:
Session 6
Electricity: Review
Management:
Building an Integrated and Comprehensive Compliance Program for Sustainable
Value
Hacking
History:
Mitnick, Wozniak, and Draper (Captain Crunch) The
Captain Crunch cereal-box whistle that shut down AT&T.
Current Events:
The Pringles can WI-FI antenna for intercepting
corporate secrets and utilizing others' software
Vocabulary: None
Other:
Session 7
Electricity: Review
Management:
Risk Assessment
Hacking History:
Video: Microsoft vs. Apple -
Pirates of Silicon Valley
Current Events: Zombie Computers
Vocabulary: words assigned
Other:
Session 8
Electricity: The Solar Winds - a hacker's best friend
Management:
Managing Antifraud Programs and Controls
Hacking History: 60 Minutes: The Internet is Infected
Current Events: Hacking vending
machines
Vocabulary: None
Other:
Session 9
Electricity: Cell Phones
Management:
Codes of Conduct, Communication, and Training
Hacking History:
Hacking and Protecting Cell Phones
Current
Events:
Vocabulary: words assigned
Other:
Session 10
Electricity: The Earth's Magnetic Fields - Switching
Polarity?
Management: Internet
Article: Hacker Slang and Hacker Culture
Hacking History:
Iran's Nuclear Centrifuges - Who Hacked them?
Current Events:
Political and Military Hacking
Vocabulary:
None
Other:
Session 11
Electricity: Review Magnetic Waves
Management:
Hacking History: Can
Online Piracy Be Stopped by Laws?
Current Events:
Relationships, Community, and Identity in
the New Virtual Society
Vocabulary: words
assigned
Other:
Session 12
Electricity:
Management: Auditing and
Monitoring
Hacking History: Video: Hackers
are People Too (an introduction to the hacker's personality and thought
process)
Current Events:
Hacking Banks - a Very Popular Pastime
Vocabulary: None
Other:
Session 13
Electricity:
Management: Mechanisms for Reporting
Fraud and Misconduct - Whistle Blower Policy
Hacking History:
Operating and Hacking Government Drones
Current Events:
Is The United States Government Spying on You? Does the US Government Care More About Spying On
Your Email Than Getting You A Job?
Vocabulary: words assigned
Other:
Session 14
Electricity:
Management: Protecting Personal and
Company Websites
Hacking History: The Ten
Greatest Hacks of All Time - Part 1
Current Events:
The Latest Hacking Gadgets to Threaten your Identity and Property
Current Events:
Some video gadget fun
Vocabulary: None
Other:
Session 15
Electricity:
Management: Me and My Data: How Much
Do the Internet Giants Really Know?
Hacking History: The
Ten Greatest Hacks of All Time - Part 2
Current Events:
Know Your Rights for Search and Seizure Laws for Data
Vocabulary: words assigned
Other:
Session 16
Electricity:
Management: A Model for Managing
Fraud and Misconduct
Management: Ransomware
Hacking History:
Hacking Identity Theft
Vocabulary: None
Other:
Class Party
Electronic Crime in Today's Society
Fall 2017
Maplewood Career Center
Detailed Course Syllabus
-
HELPFUL TOOLS:
Hacker Dictionaries
Hacker's Dictionary
FOLDOC Dictionary
Enter your term on the
top and click search.
The Jargon File
Click on "Glossary" in Section II on the left hand side.
-
POWERPOINT PRESENTATIONS
Atoms, Energy, and
Electricity Part I
Atoms, Energy, and Electricity
Part II
Atoms, Energy,
and Electricity Part III
Atoms, Energy,
and Electricity Part IV
Text Books
Technologies, Social Media, and Society - 13/14 Edition or the Twentieth Edition
Managing The Risk of Fraud and Misconduct
- McGraw Hill
Session
1 -
Monday, September 25, 2017
-
6:00 pm to 9:00 pm
Readings: First Assignment - Read
before coming to class:
Technologies, Social Media, and Society – Read Article 1 in 13/14
edition; Article 1.1 in Unit 1 from the Twentieth Edition: Five Things
We Need to Know About Technology
There will be a class discussion on this important article.
Class Lecture:
You will learn about what happens in our society when major technological
advancements occur - who is benefited and who is harmed. You will be introduced
to your first list of Electronic Crime vocabulary words and you will begin your
study into the characteristics of electricity that allows criminals to steal
money and data.
Telecommunications hacking, called phreaking - the introduction to hacking for
many early criminals, will be reviewed.
Class Lecture:
Atoms,
Energy, and Electricity - Part One
PowerPoint:
(PowerPoint Presentation -
Atoms, Energy, and
Electricity Part I)
Videos:
"MCI - The Invisible Criminals"
Vocabulary:
Virus
Worm
Hacker
Trojan Horse
Cracker
Social Engineering
Phreaker
Firewall
Backdoor
Dumpster Diver
Session 2 -
Wednesday, September 27
Readings:
Technologies, Social Media and
Society,
"Five Things We Need to Know About Technology Change"
Class Lecture:
Class Discussion from our last class:
Technologies, Social Media and
Society, "Five Things We Need to Know About Technology Change"
The word processing, spell checking, grammar correcting PC was a blessing
to writers and students everywhere. However, typewriter companies went out
of business and our children are not learning how to spell. The hand-held
calculator was a God send over the slide rule. The calculator was small and
easy to carry, helped people calculate the best bargains at a grocery store,
helped engineers to do complex calculations on job sites, and made math
calculations a breeze for students increasing their accuracy. However, our
children's mathematics skills are shrinking.
In the olden days oil was used in lamps to provide light for our homes.
When the electric light bulb was invented, it should have put the oil
companies out of business, but the invention of the oil furnace kept them
alive. When the natural gas furnace was invented the oil companies should
again have seen their demise, but the invention of the automobile and
airplane saved them again as gasoline provided a new demand. What will
happen to the oil companies when solar and electric cars are perfected?
You are going to school on line using your PC for this course? A few
years ago the only school available was a classroom or a correspondence
course where individual lessons were delivered to you through the mail.
Correspondence course companies are now out of business. Some colleges are
closing their doors or offering on line courses and remote learning sites
to compete with the changing demand for education.
Using any two of the Five Things We Need to Know About
Technology Change, describe a product or service in your life, family,
or job that illustrates a clear example of your two choices.
Class Lecture:
Management: You will be
introduced to different types of insider crime occurring in corporations.
Managing the Risk of Fraud and Misconduct
Part I –Understanding Fraud
Chapter 1-Asset Misappropriation
PowerPoint:
Atoms, Energy, and Electricity - Part Two (PowerPoint Presentation -
Atoms, Energy, and Electricity
Part II
Videos:
Vocabulary: None
Managing the Risk of Fraud and Misconduct – Read
- Part I – Chapter 2 - Financial Reporting Fraud
Session
3
- Monday, October 2
Readings:
Big
Brother is Here and His Name is Facebook
Technologies, Social Media, and SocietyRead Article 5 in the 13/14 Edition, and Article 3.2 in
the Twentieth Edition. What Facebook Knows.
Read Article 4 in the 13/14 Edition, and Article 5.2 in
the Twentieth Edition: How Google Dominates Us
Class Lecture:
Current Events:
Facebook and Google
This week will take you into some of the problems and future
concerns with your social networks, like Facebook. Are we being manipulated and
controlled? Is all of our personal information on Facebook, now the largest
human behavioral data base in the world, going to cause us problems in the
future? Will our private and highly personal information be sold or compromised?
Our smartphones, are they actually making decisions for us like which movie we
want to watch, which restaurant do we want to go to, and which products or
services are we going to use? Are all our Internet clicks recorded? Is our
location always available to someone through GPS recorded tracking?
Find the section titled "Social Engineering"
and described how Facebook was used to secretly increase organ donors and
influence elections by getting more people to vote. Discuss how do you feel about the possibility of Facebook or
other social media being used to secretly influence your
choices? Do you feel you are being unknowingly manipulated if
this technique was used to sell products or influence your
social or political decisions? Has this happened to you?
Class Lecture:
Management: Reporting Financial Fraud, the Fraud
Triangle
Corporate fraud will be explored again, but
this time through financial reporting fraud. Can money be stolen from a
corporation by minipulating expense and revenue figures? Since 80% of corporate
fraud occurrs from employees, are top management as involved as other
lower-stature employees?
Asset Misuse
Noncash Fraud
Asset Requisition and
Transfer Fraud
Larceny
Lapping
Fraudulent Billing
Payroll Schemes
Skimming
Ponzi Schemes
Class
Lecture:
Electricity:
Radio Waves;
Ohm's Law - Charge,
Current, Voltage, and Resistance
Ohm's Law: As we advance our way toward understanding how
magnetic signals carrying personal information are intercepted and stolen by
hackers, we will explore voltage, amperes, and resistance through Ohm's Law.
This involves only simple arithmetic like 6=12 / 2 or 12 = 6x2. For those of
you afraid of math, we go no further than Ohm's law.
Ohm's Law
Mysterious Magnetic Fields 1:38
Basic DC Series Circuit 4:23
Simple Series and
Parallel Circuits 8:35
Class Lecture:
Hacking History: RFID Wallets and
Readers (Radio Frequency Identification)
PowerPoint:
Atoms, Energy,
and Electricity Part III
Videos:
Magnitisim: view the following short
videos designed to help you understand this material.
AC & DC
Resistance
What is electricity
Ohm's Law
Vocabulary:
ISP
Shoulder Surfing
Twitter - What is this
organization; what does it do?
Facebook - What is this
organization; what does it do?
Bit
Byte
Barf or
Barfulation
Code Police
CEO - See Chapter 2 in
Managing the Risk of Fraud and Misconduct
U.S. GAAP -
See Chapter 2 in Managing the Risk of Fraud and Misconduct
Session 4 -
Wednesday, October 4
Readings:
Managing the Risk of Fraud and Misconduct
- Falsifying Government Claims and Insider
Trading - Pages 83-88
Class Lecture:
Discussion: If you understood the presentation Atoms, Energy, and Electricity Part
III then you have a remarkable knowledge about an incredible phenomenon that
we use hundreds of times a day, but had no idea about its complexity.
Thousands of electromagnetic waves are passing through our bodies from
all the radio and television signals, everyone's cell phone conversations,
everyone who is texting, all Wi-Fi locations, all police cars, fire trucks,
and ambulances, all aircraft, the military, gamma rays, ultraviolet,
infrared, and thousands of others. It's very good we can't see these
electromagnetic waves because there are so many of them we wouldn't see much
of anything else.
With much of our personal and proprietary information available through
the interception of electromagnetic waves, are you a little nervous about
your credit cards, bank accounts, securities, and other personal
information? Can your medical records be easily hacked? Can money from your
checking accounts be transferred in the middle of the night while you sleep?
While your bank manager is at her desk entering bank account and credit
card numbers of customers into her computer, someone in a van stopped in the
bank's parking lot is busy intercepting these signals and stealing all this
data. You see, every time the bank manager strikes a key on her
computer keyboard, it sends an electric signal to the computer and the
computer screen. Did I say an electrical signal was sent? Yes, and it
created a electromagnetic wave as all electrical signals do, and this
electromagnetic wave left the bank manager's key board and traveled through
space at the speed of light. Yes, the van in the parking lot has an antenna
(wire, conductor) that picks up these electromagnetic waves from the bank
manager's keyboard turning them into alternating currents that can be tuned
to duplicate each key stroke, each password, each bank account code, and
each credit card number.
There are companies that do not have enough computer space to manage
their operations. Instead of spending thousands of dollars on more computer
memory and operating software, they intercept the computer Wi-Fi signals
from other companies and actually utilize their unused computer memory,
storage space, and even software. The best kind of antenna for intercepting
computer system Wi-Fi signals is made from an empty Pringles potato chip
can. The Pringles can has aluminum foil on the inside that creates
alternating electric currents when passed over by a company's Wi-Fi
electromagnetic waves traveling from their router through space at the speed
of light. Feel safe?
Discuss in class how
understanding the electromagnetic wave phenomenon presented in my PowerPoint
presentation Atoms, Energy, and Electricity Part III made you feel? Is
this a revelation to you? Did you already know this? Are you feeling nervous for
your security? Are you worried about Identity theft?
Class Lecture:
Electricity: Induction
AC Current Through Magnetism
Electromagnetic Spectrum Source: Rocketboom.com
Electrometric Waves and the Sun Source: PBS Video
The Earths Magnetic Lines of Flux Source: Youtube.com
Class Lecture:
Management:
Falsifying Government Claims and Insider
Trading - Pages 83-88
Class Lecture:
Current Events: Creating Safe Passwords
PowerPoint:
Atoms, Energy,
and Electricity Part IV
Videos:
Hacking History: Kevin Mitnik
Kevin Mitnik from Takedown
Live on the Web - Kevin Mitnik
Vocabulary: None
Session 5 -
Monday, October 9
Readings:
Read the following articles from the Internet:
How to recognize phishing email messages, links, or phone calls
Protect yourself from cybersquatting and fake web addresses
Class Lecture:
Discussion
- How Modern
Technology Has Negatively Impacted Your Life
Almost all of you have been
exposed to the problems associated with electronics in the workplace. This
class deals with how electronics (computers, software,
pagers, cell phones, laptops, e-mail, Bloggs) improperly
implemented into the workplace causes stress, turnover,
poor moral, loss of efficiency and effectiveness,
undermined corporate structure, and encourages internal
crime. Your class discussion should involve your personal
experiences with this problem. By understanding how and
why these things occur, you will hopefully become better
managers.
If you are a housewife or househusband and have never
experienced the negative aspects of electronics in the
workplace, perhaps your social contacts have unfavorably
changed for the same reason. Many persons have
lost friends because of excessive participation with
American on Line (AOL). Chatting on AOL, being
addicted to their garage sales, addicted to computer
games with partners in remote locations, or just surfing
the Internet have so involved some families that their
friends and other former social contacts have all but
been replaced with these new electronic acquaintances.
Have you ever been the victim of identity theft?
Children spending hours on the Web have altered family
social activities. Perhaps your children have had
unpleasant experiences associated with the total
proliferation of adult material. Possibly you have
become the victim of computer fraud over the Internet.
Perhaps electronics in your social circles have had a negative impact on your
morale, self-esteem, or social standing. Have you ever been the victim of
bully texting? Perhaps an electronic dating service has exposed you to a less
than desirable experience.
Class Lecture:
Electricity: Transformers
How Transformers Work 1:55
Class Lecture:
Current Events: Phishing and
cybersquating
PowerPoint: None
Videos:
Hacking History:
Hackers
Class Lecture:
Discussion:
Towards the end of the movie Hackers, a war was
waged on the main frame computer designed to sink the oil tankers by
hundreds of computers from all over the world attacking simultaneously. What
is the hacker term for this type of an attack?
You have been told in
this course that 80% of corporate electronic crime comes from insiders. How
does this fact pertain to the filmHackers? Do you see any similarity
between the movie Hackers and the Kevin Mitnik story?
Vocabulary:
Botnets
Wall (as used on Facebook) Uploading
Downloading
Uploading
Browser
Phishing
Spy ware or malicious software
Cybersquatting or Typosquaters
Blog
Brain dump
Session 6 -
Wednesday, October 11
Readings:
Class Lecture:
When automation at the workplace
started in the 1950s and 1960s, many people projected that the use of computers
would allow a person to do one days work in only three or four hours. This would
greatly increase the worker's leisure time. As it turns out, when computers did
allow one worker to finish his/her tasks in a few hours, instead of going home,
the worker was told to stay at work doing the tasks of two or three workers.
This not only increased each worker's responsibility, but reduced jobs.
Employers now had a better means to spy on employees through technology. This
topic will gradually be covered throughout the rest of this course.
What is Phishing? How can we detect it? What is Cybersquatting? What is
Social Engineering? Are we ever personally exposed to these activities? Can
these activities be spotted by us, the users, before and damage is done to our
computers or bank accounts?
The
above topics will be studied this week along with getting closer to
understanding how criminals intercept our computer and cell phone signals. Read the Hacker Newspapers listed
below. Are your cell phone
conversations being recorded? Are your cell phone numbers being compared to
those phone number called on terrerist's cell phone records?
Class Lecture:
This week we
will better understand how cyber criminals intercept proprietary
information like passwords, credit card numbers, and transferring money from
bank accounts. It is interesting to note that one rarely reads in the
newspapers or views on TV news programs stories about money being stolen
from banks through hackers and cyber criminals, yet this type of electronic
crime is very common. If you were the CEO of First National Bank and your
customers were having money stolen from their accounts by hackers, would you
want that published in a newspaper or on the TV news? Probably not, for many
of your customers would close their accounts. If the police located a cyber
criminal hacking into your customer's accounts, would you want that person
arrested and prosecuted so all the details about the trial would be in the
newspapers or on the evening news? Again, your bank would lose many
customers.
People today are so use
to texting, using email, participating in chat rooms and other forms of data
communications that it is often difficult to tell if your friends or
associates are real people. Are these continuous cyber relationships harming
our social person-to-person interaction skills? Is the person we are
communicating with who they say they are or, possibly, even real?
In order to protect our companies and employers we need to be familiar with
building or maintaining an
integrated and comprehensive
compliance program capable of assessing risks, preventing and detecting
misconduct, and evaluating its effectiveness. After all, being aware of
electronic crime, preventing and detecting it, and improving policies and
procedures to prevent its recurrence is probably why your are taking this
course.
PowerPoint:
Videos:
Vocabulary: None
Session 7 -
Monday, October 16
Readings:
"How Zombie Computers Work" by Jonathan Strickland
http://computer.howstuffworks.com/zombie-computer.htm
Class Lecture:
Current Events: Zombie Computers
"How Zombie Computers Work"
Class Lecture:
Management:
Risk Assesment
Class Lecture:
Electricity: Review
PowerPoint: None
Videos:
Hacking History:
Video: Microsoft vs. Apple
-
Pirates of Silicon Valley
We will explore the development of
Microsoft Corporation and Apple Computer starting will Bill Gates and Steve Jobs
in their college dorm rooms all the way up to the major corporations they
created. How did they compete or cooperate? Were they ethical to each other? A
surprising look at these two technological giants makes a fascinating study for
this course. Discuss what you
thought of the apparent lack of open ethics between Steve Jobs and Bill
Gates as their businesses started to become major corporations? Were
you surprised? Who did you think exercised fewer scruples, Steve Jobs or
Bill Gates? It is interesting to follow Steve Jobs and Steve Wozniak
from their hacking days with Captain Crunch to forming one of the most
profitable corporations in the United States. Did you notice how they
treated Xerox to obtain their secrets? Was that ethical in your opinion? Did
Bill Gates display similar questionable behavior in any of his dealings with
other companies?
Vocabulary:
Risk-Specific Compliance Managers - See Chapter 6 - Managing the Risk
of Fraud and Misconduct
Frequency
Wavelength
Virtual Reality or Virtual Society - Article: Relationships, Community,
and Itenity In the New Virtual Society in the text Technologies,
Social Media, and Society
Micro-Coordination - Article:
Relationships, Community, and Itenity In the New Virtual Society in the
text - Technologies, Social Media, and Society
Gabriel
Gnarly
Clone
Fried
Iron Box
Session 8 -
Wednesday, October 18
Readings:
Class Lecture:
Electricity: The Solar Winds - a hacker's best friend
Some hackers have threatened to take down the national power
grid in order to shut down the Internet and create havoc around the world.
Did you know that the national power grid can also be shut off by the solar
winds mixing with the earth's magnetic field? Did you also know that our
earth would be uninhabitable without the earth's magnetic field? This
magnetic field stuff is very important in addition to being fascinating.
Preventing fraud from a manager's perspective through codes of conduct will
be introduced. This is probably one of the reason you took this course, not
only to learn about the many forms of electronic crime, but to finds ways of
reducing such activities to protect your company.
The Solar Winds and Our Magnetic Field 4:44
The Earth's
Magnetic Field is Collapsing 3:39
The Solar Winds
Effect on Earth 4:44
Class Lecture:
Management:
Managing Antifraud Programs and Controls
Managing Antifraud Programs and Controls by the American
Institute of Certified Public Accountants, Inc. New York, NT.
PowerPoint: None
Videos: Hacking History:
60 Minutes: The Internet is Infected
Current Events: Hacking vending
machines
Fraud in vending machine hacking
Hacking a pop machine 0:54
Vocabulary: None
Session 9 -
Monday, October 23
Readings: Managing the Risk of
Fraud and Misconduct - Chapter 8- Codes of Conduct, Communication, and
Training Pages 139 through 15
Class Lecture:
Management:
Codes of Conduct, Communication, and Training
Class Lecture:
Electricity: Cell Phones
Class Lecture:
Hacking History:
Hacking and Protecting Cell Phones
PowerPoint:
None
Videos:
60 Minutes - IPhone Hack
Police crack mass-arrest cell phones during Trump campaign
Has
your smart phone been hacked?
How easy is it to hack a smart phone?
How safe is the Cloud?
Vocabulary:
Many of the below terms were taken from articles in
Technologies,
Social Media, and Society. Please understand the definition,
not just what the letters stand for (like PDF).
Blue Box
Malware
Encryption
Slammer Worm
U.S. Power
Grid
PDF Files
Denial of Service Attack
ESN / MSN
War
Dialer
USB
Session 10 -
Wednesday, October 25
Readings:
Hacker Slang and
Hacker Culture Click to read article
Technologies, Social Media, and Society:
- In Edition 13/14, read article 17, and in the
Twentieth Edition read Article 4.1: Hacking The
Lights Out.
- In Edition 13/14 read Article 18 and in the
Twentieth Edition read Article 8.3: Bride of
Stuxnet.
Class Lecture:
Electricity: The Earth's Magnetic Fields - Switching
Polarity?
The earth's magnetic fields when struck by the solar
winds from the sun can shut down the power grids in many
countries. It sounds like the sun can perform some very
sophisticated hacking! What do you think of all this?
Protecting ourselves from hackers and cyber-criminals is
difficult enough, but how do we protect ourselves from the
solar winds? Many hackers have proclaimed, some testifying before
Congress, that the easiest way to shut down the Internet is
to hack into and disable the nations power grid. No electricity to
homes and business, no Internet. Are you seeing how mysterious and powerful
magnetic fields can be?
The Solar Winds and Our Magnetic Field
The Earth's Magnetic Field
Class Lecture:
Hacking History:
Iran's Neucular Centrifuges - Who Hacked them?
Is it possible to hack a virus
into Iran's nuclear program and cause severe physical damage to over
1,000 of their nuclear processing centrifuges? While these centrifuges
are being ripped apart is it possible to send signals to all the
monitoring and control stations that everything is operating normally?
Well, this happened. In fact, finding who was responsible was on the
news two weeks ago - June 2013. The virus is named Stuxnet, and it
quickly spread to over 100,000 computers in Iran's nuclear program
before it was stopped. Who did this? The United States? Israel? If
Stuxnet appears to be a highly sophisticated virus, it's nothing
compared to the one that hit Iran's oil industry in April 2013 called
Flame. Are wars going to be fought this way in the future? Are bombs and
soldiers going to be outdated?
Phreaker's hack into telephone systems. We are going to take a close
look at yesterday when AT&T was most vulnerable and the three most
famous phreakers of our time were driving Ma Bell and the FBI into
distraction. Apple Compouter was founded by one of those phreakers.
Class Lecture:
Current Events:
Political and Military Hacking
PowerPoint: None
Videos: The
Hacker's Home Page (This site is provided to study the
hacker community and philosophy and to make you aware of
what tools are available.)
Vocabulary: None
Session 11 -
Monday, October 30
Readings:
Class Lecture:
Electricity: Review Magnetic Waves
Class Lecture:
Hacking History: Can
Online Piracy Be Stopped by Laws?
Class Lecture:
Current Events:
Relationships, Community, and Identity in
the New Virtual Society
PowerPoint:
Videos:
Vocabulary:
Fourth Amendment
File sharing
Domain name
URL
First
Amendment
ISP Memorandum
Time-shifting-
Whistle
blower - Chapter 10
Exit Interviews - Chapter 10
Web-based
reporting system
Session 12 -
Wednesday, November 1
Readings:
Class Lecture:
Management: Auditing and
Monitoring
Your organization should establish auditing and monitoring of all company
transactions to help insure that fraud and misconduct does not occur, or if it
does, that it be detected. How does one set up such a auditing and monitoring
system?
Class Lecture:
Current Events:
Hacking Banks - a Very Popular Pastime
PowerPoint: None
Videos:
Hacking History: Video: Hackers are People Too (an
introduction to the hacker's personality and thgougfht process)
John T Draper, known as Captain Crunch, was the nickname of a
hacker in the 1970s who shut down the eastern half of AT&T's
telephone long distance switching system. He accomplished this task
by blowing a whistle found in a Captain Crunch cereal box into a
telephone. The frequency of the whistle was about 2600 cycles per second, or
as we now know, 2600 Hz. 2600 Hz is well within the range of human
hearing being between 20 Hz up to 20,000 Hz. Do you remember that one of the hacking organizations in New York
listed each week on our schedule is called 2600? I wonder why they
use that name?
AT&T decided to save money by allowing their voice and data
signalling frequencies to be in the same frequency range. A 2600 Hz
tone is a little higher in pitch than a dial tone and was used by
AT&T's long distance switching stations to look for an open long
distance line. Empty or unused long distance lines would look for a
newly dialed long distance call that needed to be connected to the
long distance network. AT&T's equipment generated a 2600 Hz tone
when a long distance call was placed and the AT&T switching station
looked for lines generating this tone. Once located, the
switching station connected the call generating the tone to the long
distance network and completed the call. It turns out that the Captain Crunch whistle found in the cereal
box generated an almost perfect 2600 Hz tone. Guess what happened?
Go to the links below and learn about Captain Crunch. Learn about
the relationships of Captain Crunch (Draper) with Kevin Mitnick,
Steve Jobs and Steven Wozniak from Apple Computer (small world).
Discuss what do you think of a cereal whistle being used to shut
down AT&T? In a previous week, I mentioned that an empty
Prinkle's Potato chip can was an excellent antenna for intercepting
corporate Wi-Fi signals and utilizing their computers.
Cereal box whistles,
potato chip cans - what's going on here?
Vocabulary: None
Session 13 -
Monday, November
Readings:
Internet Readings
Class Lecture:
Management: Mechanisms for Reporting
Fraud and Misconduct - Whistle Blower Policy
An estimated 42% of million-dollar fraud cases were originally
discovered by whistle blowers. What kind of corporate culture and
environment feels safe for employees to turn in hackers and cybercriminals
working among their ranks? Is confidentiality and security a concern? What
about the harassment of co-workers after a whistle blower revealed to
management a fraudster among the ranks? How safe is middle management with
this information? Can they be trusted?
Class Lecture:
Hacking History:
Operating and Hacking Government Drones
Class Lecture:
Current Events:
Is The United States Government Spying on You? Why Does the US Government Care More About Spying On
Your Email Than Getting You A Job? Government agencies throughout the
world are pushing for laws forcing third-party providers to collect far more
personal data on individuals than the company requires for their business needs.
In the contracts requiring the length of time this storage must be retained,
there is usually provisions for the government to have access to all records
expanding its surveillance capabilities on its citizens. (Sleep well, my
friends)
Addressing your future privacy on the Internet I'm sure is a
concern for everyone since there is very limited privacy
now. Should you use cloud, for example, by storing all your personal
information on the Internet instead of your hard drive? Is it safer than
using computer storage? Are governments creating laws that force companies
to collect far more personal data on customers than is necessary to run the
business? Are their provisions that all this data must be made available to
governments as an enhanced method for creating deepening surveillance on its
citizens? Who is the enemy here - the cybercriminals or the government?
PowerPoint: None
Videos:
Vocabulary:
Tracking files
Third-party tracking files
Beacons
Flash
cookies
BlueKai (the company)
Flux
Ampere's Law
Solar
Winds
Cyberbullying
Code of Conduct
Session 14 -
Wednesday, November 8
Readings:
Class Lecture:
Management: Protecting Personal and
Company Websites
Class Lecture:
Hacking History: The Ten
Greatest Hacks of All Time - Part 1
Class Lecture:
Current Events:
The Latest Hacking Gadgets to Threaten your Idenity and Property
PowerPoint: None
Videos:
Some Video Fun:
Electronic Gadgets
Fun with Magnetism
An Electric Motor
A
simpler motor
A Blond
Girl Motor
How to Hack a POP
Machine
Reprogram POP
Machines
Elevator Hack
Inside
a 9V Battery
Combination Lock Pick
Locked out of your
car?
Car
Lock Myth Busted
Vocabulary: None
For Next Class:
Session 15 -
Monday, November 13
Readings:
The Hacker's News
Class Lecture:
Management:
Me and My Data: How Much
Do the Internet Giants Really Know?
Class Lecture:
Hacking History: The
Ten Greatest Hacks of All Time - Part 2
Top 5 Hackers Publications, Web Sites, Etc.
Class Lecture:
Learning about hacking organizations
Cult of the Dead Cow
2600 - The Hacker Quarterly
L0pht Heavy Industries
Anonymous
Lizard Squad
The Level Seven Crew
LulzSec
The Syran Electronic Army
Global Hell
Team Poison
The Chaos Computer Club
End Note
PowerPoint:
Current Events:
Know Your Rights for search and seizure and copyright
laws
Copyright
infringements concern Web site owners, authors, music and video organizations,
writers, and many other areas where the protected origin of works are of a
concern. This is also of paramount importance to many corporations. The latest
copyright laws will be visited as well as the right of law enforcement officers
to search and seize your computers both at work and at home including the data
contained therein.
Videos:
Vocabulary:
Vocabulary from next week's reading
Best
Practices - Ransomware
Deep Web
Ransomware
Virtual patching
Zero-day exploits
PowerShell
Least privilege
Sandbox
WannaCry
Petya
Session 16 -
Wednesday, November 15
Readings:
TrendMicro:
What is Ransomware?
Best Practices - Ransomware
Class Lecture:
Management: A Model for Managing
Fraud and Misconduct
Class Lecture:
Hacking History:
Hacking Identity Theft
Class Lecture: Hacking
Conventions that you may attend held in the United States
(taken from wicipedia.com)
CarolinaCon, in
North Carolina, is a regional technology and network security conference
usually held during Spring.
CircleCityCon is a security and technology conference held annually in June
in
Indianapolis.
CypherCon, a
Milwaukee
based hacker conference held late winter each year.
DEF CON, in
Las Vegas,
Nevada, is the biggest hacker convention in the
United States held during summer (June–August).
DerbyCon,
an annual hacker conference based in Louisville, KY.
GrrCon, an annual hacker conference hosted each September in Grand Rapids,
Michigan.
Hack in the Box, an annual hacker conference.[55][56]
Hackers on Planet Earth (HOPE), in
New
York City is held by
2600: The Hacker Quarterly in mid-summer (July/August) every other year.
HackMiami Conference, a hacker conference in Miami, Florida organized by the
HackMiami
hackerspace.
INFILTRATE, hosted by Immunity, Inc, is a deep technical security conference
that focuses on offensive technical issues. The conference has been held
annually in
Miami Beach,
Florida since 2011.
LayerOne,
held every spring in Los Angeles, California.
Notacon, in
Cleveland,
Ohio, is an art
and technology conference held frequently in mid-April.
PhreakNIC,
in
Nashville,
Tennessee,
is held by Nashville 2600. around October.
Quahogcon, In
Providence,
Rhode
Island is held at the end of April.
ShmooCon,
a
Washington DC convention started in 2005 by
The Shmoo Group, and held annually in late winter (usually February).
SkyDogCon, A technology conference in Nashville, TN for the individual with
the Renaissance Mind. SkyDogCon exists to facilitate learning, information
sharing, and mingling with like-minded people in a relaxed atmosphere.
Summercon,
one of the oldest hacker conventions, held during Summer (frequently in June).
It helped set a precedent for more modern "cons" such as H.O.P.E. and DEF CON.
T2 infosec conference, focuses on newly emerging information security
research with a balance of topics on auditing and pen-testing, and security and
defensive strategies. In general, presentations will address different aspects
of information security—all presentations will include demos and be technically
oriented and practical.
THOTCON, a
Chicago
based hacker conference held in the Spring each year.
ToorCon, San
Diego hacker convention that emerged from the 2600 user group frequently in late
September.
WildWestHackinFest, a conference focused on training and development held in
Deadwood, South Dakota in October. Explore the
Black
Hills and learn how to hack all the things, including the
IoT.
Videos:
Final Class Party
Supplemental Course Study Material
Hacker Web Sites &
Culture
Class PowerPoint
Presentations
Telecommunication's
Crime Presentation
Atom
& Electronics Presentation
Atoms, Energy, and Electricity
The Particle Adventure
http://particleadventure.org/particleadventure/index.html
The Story of Kevin Mitnik
Kevin Mitnik Site
http://www.takedown.com/bio/mitnick.html
The Story of the Captain Crunch Cereal Whistle
Captain Crunch
Hacker Manuals and Instruction Guides
http://www.spectre-press.com/
The Hackers' Home Page
http://www.hackershomepage.com/
Some Hacking Organizations
http://www.yahoo.com/Computers_and_Internet/Security_and_Encryption/Hacking/Organizations/
Famous Hacked Web Sites
http://dir.yahoo.com/Computers_and_Internet/Security_and_Encryption/Hacking/Hacked_Web_Sites/
Glossary of Computer and Internet Terms
http://foldoc.org/
The Hacker Dictionary
http://www.hacker-dictionary.com/
The Jargon File
http://www.catb.org/~esr/jargon/
QUIZZES
IF APPLICABLE
Electronic Crime
Fall – 2014 – LCCC and Tri-C
Quiz One
NAME (printed or typed)
_____________________________________________________________
The Five Things We Need To Know About Technology
Change
1. All technology change and
advancement is a tradeoff. This means: (5 Points)
2. The advantages
and disadvantages of a new technology are never distributed evenly among the
population. This means: (5 Points)
3. Embedded in every technology
there is a powerful idea, perhaps two or three powerful ideas. These ideas
are often hidden from our view because they are of a somewhat abstract
nature. But this should not be taken to mean they do not have practical
consequences. This means: (5 Points)
4. Technology change is not
additive; it is ecological. This means: (5 Points)
Managing the Risk of Fraud and Misconduct
5. Select the best answer: The sun will always rise
in the east and when it does we will call it morning. The sun will always
set in the west and when it does we will call it evening. This has always
been; it is part of nature - it is mythic. When a technology becomes mythic:
(3 Points)
Select one:
a. It is always dangerous because it is then
accepted as is
b. It is not easily susceptible to modification or
control
c. It is perceived to be part of the natural order of things
d. It tends to control more of our lives than is good for us
e. All of
the above
f. None of the above
6. "The printing press
annihilated the oral story-telling tradition; telegraphy annihilated space,
television has humiliated the printed word; the computer, it seems, is
degrading family and community togetherness." Which of the Five Things We
Need To Know About Technology is this an example? (3 Points)
Select one:
a. There is embedded in every great technology and epistemological,
political or social prejudice.
b. There is always a price for technology
c. There are always winners and losers
d. Technology change is not
additive; it is ecological; that is, it changes everything.
e.
Technology tends to become mythic, that is, perceived as part of the natural
order of things.
7. The three conditions that must be present for
fraud to occur are: Select one: (3 Points)
a. Opportunity, incentive, and
cooperation
b. Cohering, pressure, and opportunity
c. Opportunity,
incentive, and rationalization
d. Rationalization, opportunity, and
collaboration
e. None of the above
8. Select the best answer.
The previous question dealt with three conditions to occur necessary for
fraud. These three conditions are known as: (3 Points)
Select one:
a.
The Fraud Triangle
b. The Three Incentives for Crime
c. The Triple
Paradigm of Fraud
d. The Asset Misappropriation Trisector
9.
Select the best answer: The American Institute of Certified Public
Accountants has labeled "what" as the Achilles' heel of fraud prevention? (3
Points)
Select one:
a. Computer password hackers
b. Management
override
c. Lack of accounting control supervision
d. Computer
maintenance down time
e. The constantly changing accounting policies
requiring software updates and opportunity for hackers
10. Match the
best definition that most accurately applies to the term. Enter the letter
of the term in the blank preceding the definition. (3 Points each, total 27
Points)
I) ____The misappropriation of cash from an organization
prior to being recorded
II) ____The misappropriation of cash from an
organization after it has been recorded
III) ____Crediting one account
with the receipts intended for a different account
IV) ____Where funds
are distributed under the guise of a legitimate payment for invoiced goods
or services. Personal purchase schemes, non-accomplish vendor schemes,
schemes involving shell companies
V) ____Fraudulent disbursements that
are perpetrated through the creation of false documentation
VI)
____Placing orders for inventory that exceed the amount actually needed to
complete the project
VII) ____Fraudulent business ventures where
investors are paid from other investors' funds rather than operations
VIII) ____When an employee engages in the unauthorized use of company assets
IX) ____Inventory theft, Fictitious Sales, Purchasing and Receiving
Fraud
A. Asset Misuse
B. Noncash Fraud
C. Asset Requisition and
Transfer Fraud
D. Larceny
E. Lapping
F. Fraudulent Billing
G.
Payroll Schemes
H. Skimming
I. Ponzi Schemes
PowerPoint Slides on Electricity
11. a. Like charges _____________ each other.
b.
Opposite charges ____________each other. (4 points)
12. a. Every time
there is an alternating electric current, an _______________
_________________ is created. (2 Points)
b. Every time an alternating
magnetic field crosses a conductor, an _________________ ______________
__________________ is created. (2 Points)
c. This
______________________ ______________________ leaves the conductor and
travels through space at the speed of light. (2 Points)
13. True or
False An atom is composed of a nucleus containing positively charged
protons, negatively charged neutrons, and is orbited by neutrally charged
electrons. (2 Points)
14. True or False The carrier particle foe the
electromagnetic force is the electron. (2 Points)
15. True or False
The flow of electrons in a wire, amperes, and current are basically the same
thing. (2 Points)
16. What is a wavelength (in your own words)? (5
Points)
17. What is a frequency (in your own words)? (5 Points)
ESSAY:
18. In 500 words: How do you feel about the possibility of Facebook or other
social media being used to secretly influence your choices? Do you feel you
are being unknowingly manipulated if this technique was used to sell
products or influence your social or political decisions? Has this happened
to you? (12 points)
Electronic Crime
Quiz Two
Chapter 6
- Building an Integrated and Comprehensive Compliance Program for
Sustainable Value
Select the best answer.
1.
Effective fraud and misconduct risk management should begin with:
a. A well designed and properly executed ethics and compliance
b. A program that seeks to prevent, detect, and respond to fraud and
misconduct.
c. The program should be
thoroughly integrated into the organization's overall guidance and
risk-management framework
d. The program
should be thoroughly integrated into the company's business strategy and
operations
e. The program should not be an
isolated set of activities within the organization
f. All of the above.
Chapter 6 - Building an Integrated and
Comprehensive Compliance Program for Sustainable Value
2. Select
the best answer. Because managers, officers, and CEOs of
corporations are frequently the ones committing electronic crime, the
success or failure of a compliance program will rest on the organization's
ability to embed a culture of ethics and integrity.
Circle One: TRUE or FALSE
Chapter 6 - Building an Integrated and Comprehensive Compliance Program
for Sustainable Value
3. Select the best answer. An
affective GRC program is Government, Risk, and Compliance program that
protects, but does not enhance business values by fostering a risk-aware
culture.
Circle One: TRUE or FALSE
Chapter 6 - Building an Integrated and Comprehensive Compliance Program
for Sustainable Value
Select the best answer.
4. The
key attributes to an effective Compliance Function are:
a. Authority, Responsibility, Competency, Objectivity and Resources
b. Authority, Responsibility, Due Diligence, Objectivity, and Coordination
c. Authority, Coordination, Auditing, Responsibility, and Coordination
d. Coordination, Responsibility, Authority, Auditing, and Cooperation
Chapter 6 - Building an Integrated and Comprehensive Compliance Program
for Sustainable Value
Select the best answer.
5. An
effective Board of Directors overseeing a corporation's compliance program
needs information regarding:
a. Aligning
oversight, assessing risk, preventing misconduct, detecting and responding
to misconduct, allow the CEO to evaluate the effectiveness of the program.
b. Evaluate the effectiveness of the program by responding to the prevention
of misconduct and assigning managers to asses risking taking.
c. Aligning oversight, assessing risk, preventing misconduct, detecting and
responding to misconduct, and evaluating effectiveness of the program.
d. Aligning oversight, assessing risk, preventing misconduct, detecting and
responding to misconduct, and evaluating effectiveness of the program.
What is Alternating Current?
Matching:
6. Match the best definition in column B with the most
appropriate answer in column A.
A
B
| A. Zero |
1. ____Cycles per second |
| B. Remains constant |
2. ____Time interval between any two successive wave crests |
| C. Constantly changing |
3. ____The mazimum positive amplitude of a wave in the opposite
direction |
| D. Crests |
4. ____Maximum positive amplitude of a wave |
| E. Trough |
5. ____The amplitude of an AC current |
| F. Period |
6. ____Amplitude of a DC voltage |
| G. Frequency |
7. ____Any point along the time axis |
Article: Relationships, Community, and Identity in the New Virtual
Society
Select the best answer.
7. In this
phenomenon, relationships for young people can be just as powerful and
meaningful as those in the real world.
a.
Virtual Society or virtual space
b. The the
Internet Only
c. Chat Rooms Exclusively
d. Emailting
e. Texting above asll other mediums
Article: Relationships, Community, and Identity in the New Virtual
Society
Select the best answer.
8. When
the VCR was invented, many people predicted the demise of movie theaters;
after all, if you can watch a movie at home why would anyone pay to go out
to a theater? Today, movie theaters are doing a record business.
When video conferencing was developed, some people predicted that many
airlines and hotels would go out of business; after all, why would
businessmen spend thousands of dollars on airfare, hotels, and meals to
attend a business conference when they could stay in the office and do it on
line? Well, airlines and hotels are busier than ever.
The social turmoil of the 1970s was proclaimed by many to be the end of the
nuclear family. But the family is still here; it's just different.
People are now predicting that texting, email, chat rooms, cell phones,
blogs, Facebook relationships, tweeting, on-line dating, and other social
media are going to diminish our person-to-person interactions and destroy
human personal interaction.
What actually will
happen is some human relationships will become shallower through cyber space
relationship while others will become stronger. Things will change, but
still be meaningful. As stated in Article 1 - Technology giveth and
technology taketh away.
Circle One: TRUE or FALSE
Article: Relationships, Community, and Identity in
the New Virtual Society
Select the best answer.
9.
Your
found identity is one created by your circumstances - who your
parents were, your ethnicity, your religion, your gender, your history and
education and past experiences. Your made identity is...
a. ...the style of clothes and jewelry you wear
b. ...your chosen behaviors
c. ...your selected
automobile, activities, and clubs you have joined
d. ...how you want others to see you
e. All of
the above
Article: Are U Friends 4 Real?
Select the best
answer.
10. "Flaming" is a cyber term meaning text or
email that invokes anger or other high emotions resulting from the hostile
interpretation of such messages. But texting, email, and Facebook are
void of the human voice, the voice tone indicating anger, sadness, or
frustration; the pauses between words indicating thought or concern, and the
speed of the speech possibly indicating anxiousness.
The phrase "You can make a marketing plan," can be said many different ways
where one is a complement, the other is an insult, yet a third filled with
sarcasm. It depends on where the pauses are, where the voice volume
increases, and the voice tone. Such communication is also void of body
language and facial expressions which often make up over 80% of our personal
communications.
I once wrote what I
considered to be a very grateful email of thanks and appreciation to a
colleague for the effort he and his staff put into a wonderful weekend
wedding. Shortly after sending the letter, I received a very defensive
phone call asking how I could be so unfair and insulting when he tried so
hard to make the event successful. Somewhat dismayed, I went to his office
and read to him my email with a kind voice tone, concerned inflections,
appreciative pauses, and accompanied by facial expressions showing happiness
and gratitude. What a difference! He was amazed!
Friendships, romantic relationships, business memos, colleague
correspondence, and instructions to employees, spouses, and children are
often in the form of texts. Should care be taken in these messages to avoid
"flaming" interpretations?
a. Yes, care should always be taken to avoid "flaming
interpretations" even though success is not guaranteed.
b. No; flaming can't be avoided.
c. No, if 50
people read the same message there will be 50 different interpretations. How
can one attempt to overcome that?
d. No, email
and texting and other written forms of communication should always be
replaced with phone calls to avoid flaming.
Article: Hacking the Lights Out
Select the best
answer
11. The Stuxnet virus was planted into
Iran's nuclear program computers by:
a. Internet
virus attack through email
b. A back door attack
through a computer's firewall
c. Through a USB
stick handed to an unsuspecting employee
d.
Through the power grid at the local power station
e. From a trojan horse implanted into a didigital procedures manual
Article: Hacking the Lights Out
Select the best
answer
12. When Iran's nuclear centrifuges were spinning out of
control at a dangerous RPM, why didn't the control personnel intervene
before the centrifuges were destroyed?
a. The
virus hit the centrifuges in the middle of the night when the neclear plants
were closed
b. The virus send false signals to
the supervising controllers indicating all operations were operating
normally
c. The Stuxnet virus stopped the
control mechanisms sent to supervisory personnel.
d. The Stuxnet virus struck Iran's nuclear facilities on a holy holiday and
the plants were closed
Article: Hacking the Lights Out
Select the best
answer
13. All electricity furnished for home and industrial use
in the United States uses 60-cycle alternating current. The power grid is
the electrical supply circuits of thousands of power companies in United
States all connected together. The 60 cycle AC current coming from any power
company must match (be in sync) with the 60 cycle timing on the grid. The
Aurora cyberattack in 2007 was staged by a pretend hacker working for the
Department of Homeland Security to bring down an electric generator in a
power company attached to the grid. How did this attack function?
a. The hacker created and out-of-sync 60 cycle current in opposition
to the generators 60 cycle output.
b. The
hacker planted a bomb under the generator
c.
The hacker planted a bomb under the generator
d.
The hacker pulled the generator's circuit breaker shutting the generator
down
Article: Hacking the Lights Out
Select the best
answer
14. Computers are subject to attack.
The nation's electric power grid is also subject to attack by cybercriminals
and it is much easier to hack than many protected computers.
Circle One: TRUE or FALSE
Article The Bride of Stuxnet
Select the five answers
that apply.
15. Once the virus Flame infects a
computer, what happens?
a. It records every
keystroke
b. It creates a perfect log of all
activities
c. It takes pictures of the monitor
screen every 60 seconds
d. It sends out bogus
emails to everyone on the computer's email list
e. It takes control of Bluetooth capability turning into a hub for a
wireless network
f. It copies documents
and files on the computer's hard drive
Article The Bride of Stuxnet
Select the besat answer
16. Stuxnet was a virus designed to work quickly, and in doing so it can be
discovered quickly, so it must do its damage fast. Flame was a virus
concerned with stealth and patience, moving very slowing, and infecting
fewer machines.
Circle OneL: TRUE or FALSE
Chapter 7 - Prevention: Risk Assessment
Select the best answer
17. The definition of
what is as follows: A step-by-step process for identifying the
quantitative and qualitative nature of potential integrity breakdown?
a. Design considerations
b. Risk Assessment
c. Business goals and stategy
d. Control
Optimazion
e. Risk Taking
Chapter 7 - Prevention: Risk Assessment
Select the best answer
18. What is the below procedure entitled?
(1) Identify Business Units,
locations, or processes to assets
(2) Inventory and categorize fraud and
misconduct risks
(3) Rate risks based on likelihood and significance of
occurrence
(4) Remediate risks through control optimization
a. The four fundamental steps of risk assessment
b. The four fundamental steps of risk assessment
c. The four levels of crime, fraud, and misconduct
d. The four basics of the fraud rectangle
e. The control optimization for risk procedures
Chapter 7 - Prevention: Risk Assessment
Select the best answer
19. The first step is starting a risk assessment program is:
a. Putting someone responsible in charge
b. Deciding those aspects or parts of the organization that will be
subject to the risk assessment.
c.
Establishing a focus group to evaluate the overall risk of the company
d. Review documentation from previous risk assessment groups
e. Have the focus group consult with the risk assessment team.
Chapter 7 - Prevention: Risk Assessment
Select the best
answers - There are FOUR (4) correct answers
20. It is wise for
the risk assessment team to have a company document review take place in
order to determine company policies, procedures, and internal control.
These documents to be reviewed include:
a.
Code of Conduct
b. Applicable job
descriptions
c. Employee attendance
records
d. Organizational charts
e. Response and improvement systems
f.
Competitor's violation records
g. All of the
above
Chapter 7: Prevention: Risk Assessment
Select the best answer
21. Once the assessment team has estimated risk likelihood and significance,
it is helpful to plot risks on an axis representing their significance and
likelihood of occurrence using a heat map.
Circle One: TRUE or FALSE
Chapter 7
Secelct the best answer
22. The primary
coil of a transformer has 200 volts applied to it and 100 coils. The
secondary side of the transformer has 50 coils. What is the voltage output
on the secondary side?
a. 50 volts
b. 100 volts
c. 200 Volts
d. 100 amps
e. 4 volts
Select the best answer
23. If you cut the resistance in half in an
electrical circuit with 100 volts, the the amperes will double.
Circle One: TRUE or FALSE
Chapter 7
Select the best answer
24. If the primary input side of a
transformer has 500 turns and 100 volts, how many turns (coils) would you
need on the secondary output side for the output to be 20 volts?
a. 100 coil turns
b. 50 coil turns
c. 200 coil turns
d. 20 coil turns
e. None of the above
All your Ohm's law formulas are listed in the above
wheel.
Refer to Chapter 3 on Electricity DeMystified if necessary.
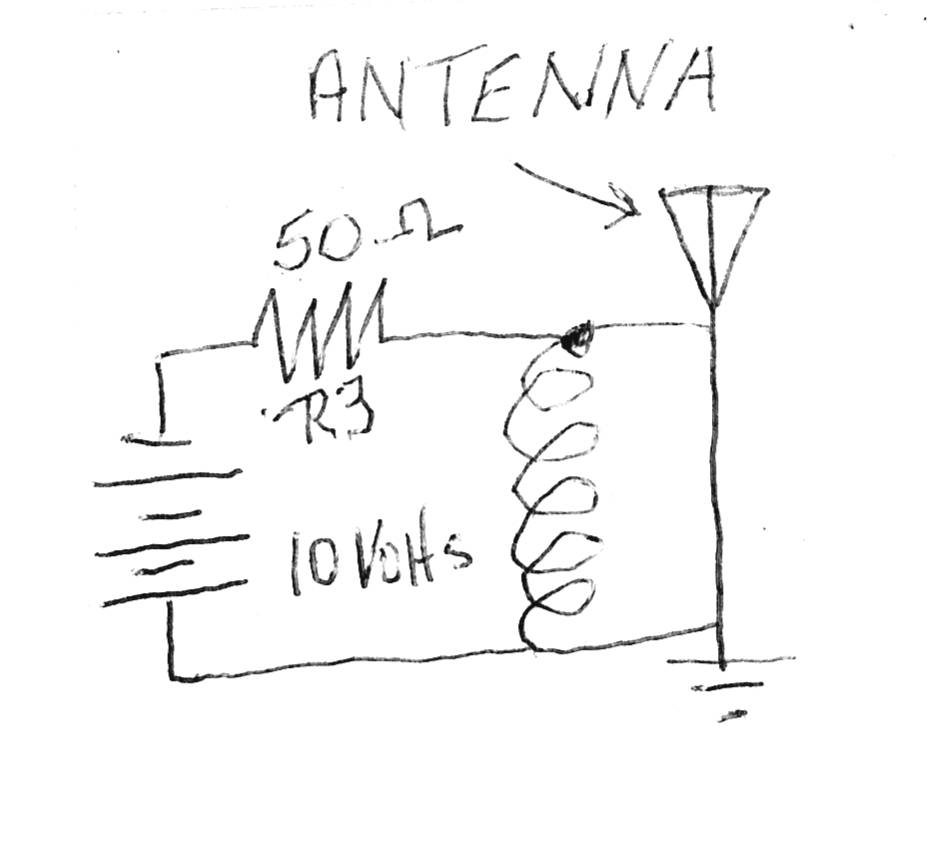
A spy for a competitive industry wants to listen to private conversations
being broadcast over a competitor's private walkie-talkie network where
management discuss test results in the field with engineers. The spy's
office is too far away to receive the competitor's walkie-talkie signals.
Somehow the spy needs to double the power output of the competitor's
walkie-talkie signal. In order to accomplish this, the spy visits the
competitor impersonating a communications walkie-talkie and radio company, J
& B Communications, offering a free introductory deal. The introductory
offer is to clean and tune all the competitor's walkie-talkies for free with
the understanding that J & B Communications would be considered for any
repair jobs in the future. The competitor agrees to the deal and give the
spy 10 walkiw talkies to be cleaned, reconditioned, and returned in the
morning. This is called social engineering.
The spy takes the walkie-talkies to his office and opens them up. The
circuit on the antenna looks like the one below.
Do not be discouraged
about this electronic circuit. Let's say it is the power output circuit to
each walkie-talkie's antenna. The power to the antenna is 2 watts.
I =
E/R = (Amps equals voltage divided by resistance)
I = 10/50 =
(Amps equals 10 volts divided by 50 ohms) = .2 amps
The
power output of the antenna is measured in watts. P = watts
P = EI (Power
equals voltage times amps)
P = 10 X .2 = 2 watts. The walkie-talkies currently
transmits a 2 watt signal. The spy wants to double this power output
to 4 watts. This would make the walkie-talkies more powerful, transmitt a
longer distance, and allow the spy to monitor his competitor's
conversations.
The spy decided to change the 50 Ohm resistor R3 in each
walkie- talkie to a different value. What value in ohms should the new
resistor be in order to double the output power of each walkie talkie?
I = E/R = (Amps equals voltage divided by resistance)
I =
10/?
= (Amps equals 10 volta divided by
?
ohms) = .4 amps
The power output of the antenna is
measured in watts. P = watts
P = EI (Power equals voltage times amps)
P = 10 X .4 = 4 watts.
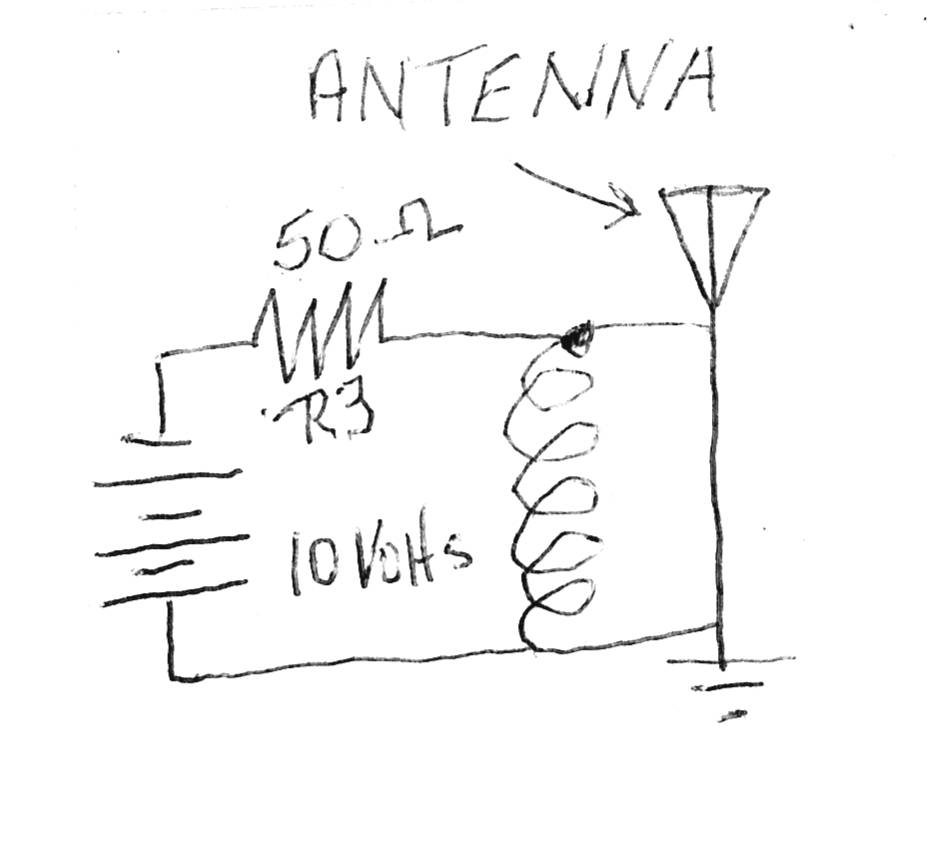
Do you see now why you learned
ohm's law? It is frequently used in electronic crime. (The actual circuit
above would require different formulas beyond the scope of this course.)
a. 50 ohms
b. 200 ohms
c. 35 ohms
d. 25 ohms
e. None of the above
Select the best answers from the matching table
26. Insert the best
answer from column A into Column B
|
A. Captain Krunch
|
___Steve Wozniak |
| B. A Hacker who helped form Apple Compluter |
___ John DFraper |
| C. A young teenager who became a phreaker and hacker |
___Kevin Mitnik |
| D. One of the founders of Apple Computer and the CEO and
chairman |
___Steve Jobs |